NEWSLETTER
The Audit Trail Has Thirty Days of Data. The Authorization Record Has Zero.
April 28, 2026
NEWSLETTER
April 28, 2026
May 30, 2026. Thirty days after Agent 365 went live in your tenant.
Your IT administrator pulls up the Agent 365 dashboard and the data is beautiful. Every agent registered. Every action logged. Purview sensitivity labels enforced. Entra Agent IDs assigned. Defender flags reviewed. The control plane Microsoft promised is exactly what it said it would be.
The administrator closes the dashboard and walks into a compliance review. The examiner asks a single question: for the agent that has been accessing your customer contract library since May 3rd, who in your organization formally decided it was authorized to do that, and where is that decision recorded?
The dashboard does not answer that question. It never did.
There is a distinction that almost nobody named clearly in the weeks before May 1st, and the silence is already costing organizations that launched without noticing it.
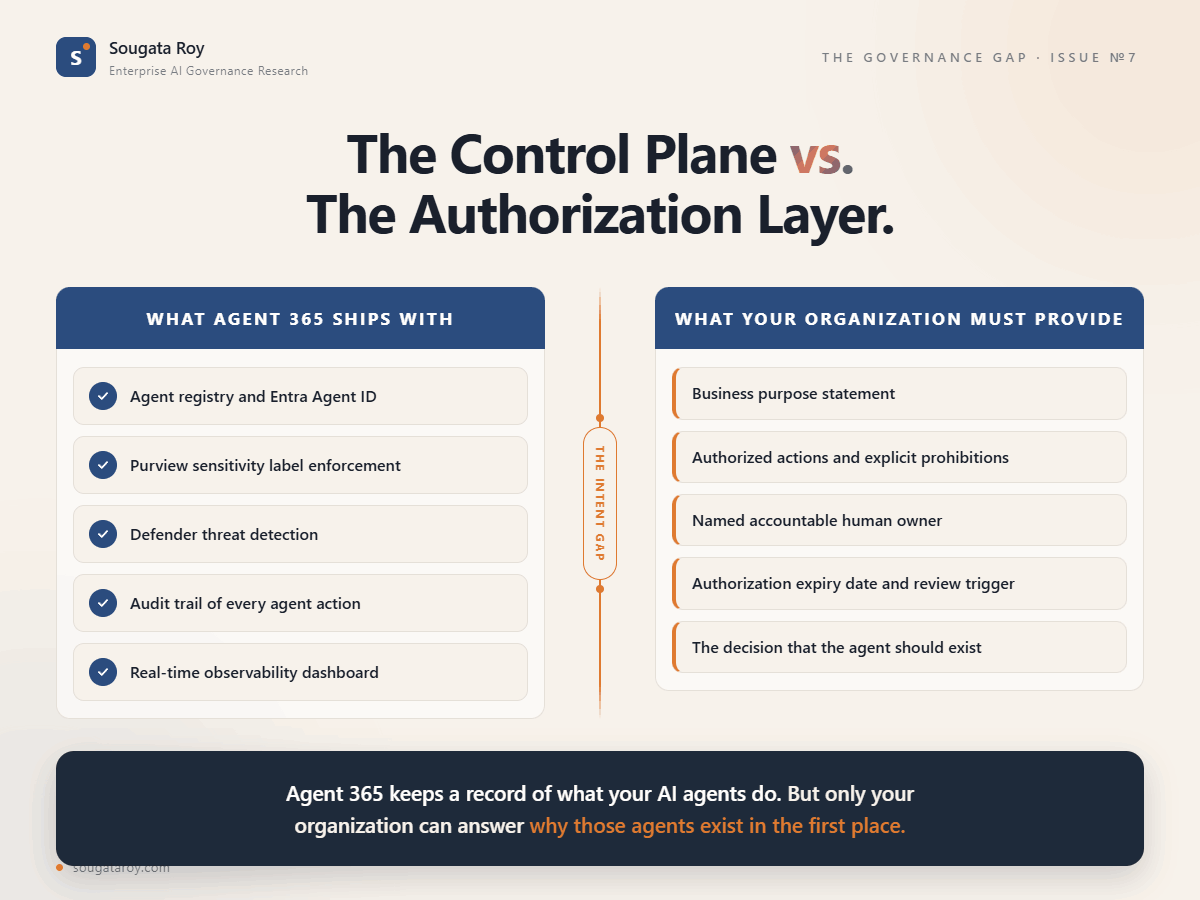
Agent 365 shipped with observability. It gives you a registry of agents, a log of their actions, a data classification layer through Purview, an identity layer through Entra Agent ID, and a threat detection layer through Defender. These are genuinely useful. The control plane works. The audit trail is real.
What Agent 365 did not ship with is an authorization record. It does not contain a field for why your organization decided this agent should exist. It does not contain a record of what was approved: the scope, the boundaries, the business justification. It does not contain a list of what the agent is explicitly prohibited from doing. It does not contain the date when that authorization expires. It does not contain the boundaries that person was made accountable for enforcing.
Those are organizational decisions. No platform ships them. They exist only if someone in your organization wrote them down before the agent went live.
Most did not write them down.
Here is what Governance Debt looks like in its quietest form.
A team deployed three agents in the first two weeks of May. The agents are working. The agents are logged. The agents are, technically, governed in every way the platform can govern them. Nobody who was not involved in building them could answer the question the examiner just asked.
Thirty days of the agents being useful is thirty days of the organization's dependence on them growing. The business process that used to take four hours now takes twenty minutes. The team that built the agents has moved on to the next thing. The agents have become infrastructure.
Now someone asks who authorized them. Now someone asks what they are prohibited from doing. Now someone asks who to call if one of them starts behaving outside the scenario it was built for.
The answer, in most organizations that launched in May without an authorization record for each agent, is silence followed by the sound of people opening Slack to find the developer who built it.
That developer left in June.
Microsoft was precise about what Agent 365 is. The product's own documentation describes it as a control plane. It observes, governs at the technical layer, and secures. Agent 365 deliberately avoids the verb "do". The platform is not about what agents accomplish. It is about the layer that monitors what they accomplish.
The accountability layer is different. It is not a monitoring question. It is an organizational design question. Who decided this agent should exist? What boundaries did that decision establish? Who is answerable when those boundaries are crossed?
Those questions have no answer inside Agent 365. They have an answer only inside the organization, and only if someone created that answer before the agent went live.
NIST's National Cybersecurity Center of Excellence, in its February 2026 concept paper on AI agent identity and authorization, called this non-repudiation: the ability to prove that specific agent actions were authorized before they occurred. An authorization record created after a problem is discovered is an incident response artifact. It is not governance evidence.
The thirty-day drift is the accumulation of agents that have audit trails and no authorization records. The ratio grows with every deployment that bypasses the document. By the time an examiner arrives, the organization has proof of what every agent did and no proof that anyone decided it should.
That is not a technology gap. Agent 365 cannot close it. It was never supposed to.
The document that closes it is two pages. Your organization either wrote it before May 1st or it did not.
The organizations that did not write it are now thirty days further from the answer an examiner will eventually require.
The document that records what the audit trail cannot is at sougataroy.com/frameworks/agent-authorization-document. PDF and Word versions. No form. No gate.
If the thirty-day drift in this edition describes your environment, the Authorization Coverage Lifecycle names the phase you are in and what the path out of it requires: sougataroy.com/frameworks/governance-debt-maturity